Part 3 – The Adversary’s Endgame: Exfiltrating a Life
In this work I will move from mapping the method of attack (the TTPs) to defining the strategic objective: what is the adversary trying to steal? In cybersecurity, “exfiltration” (TA0010) is the final goal of data theft. In coercive control, it’s the theft of a person’s life, identity, and future.
Subtitle: Mapping the Stolen “Data” in Coercive Control to the MITRE ATT&CK Exfiltration Stage.
In cybersecurity, after an adversary breaches a system, establishes persistence, and moves laterally, their final stage is Exfiltration (TA0010)—the theft of valuable data. In psychological and social coercion, the process is identical, but the “data” is infinitely more personal. The target is not servers, but a human being; the stolen assets are not files, but the core components of identity, autonomy, and destiny.
My research on the “connections in women whose lives were exfiltrated” provides the perfect dataset. We can now categorize what is stolen, why it’s valuable to the adversary, and how the theft is covered up.
The Exfiltration Goals: What Is Stolen
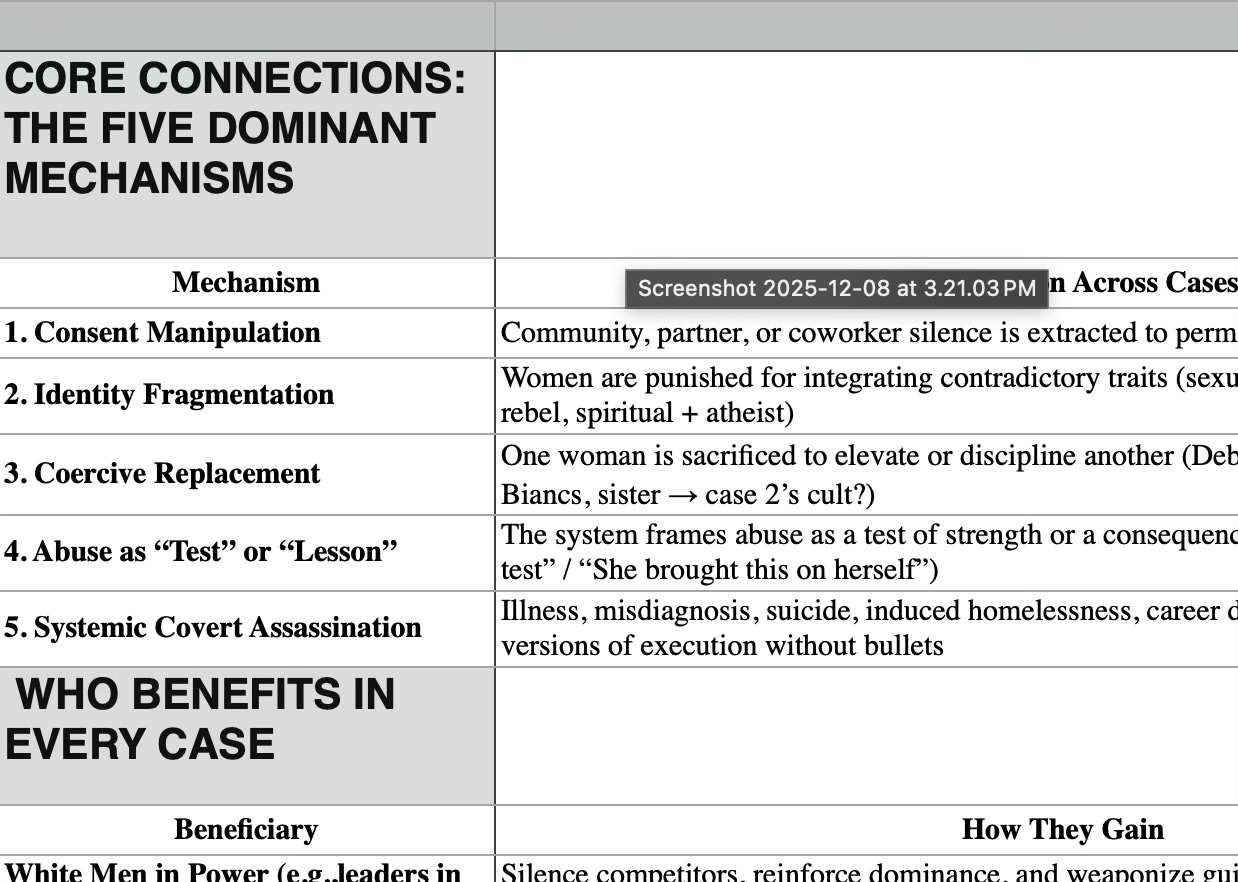
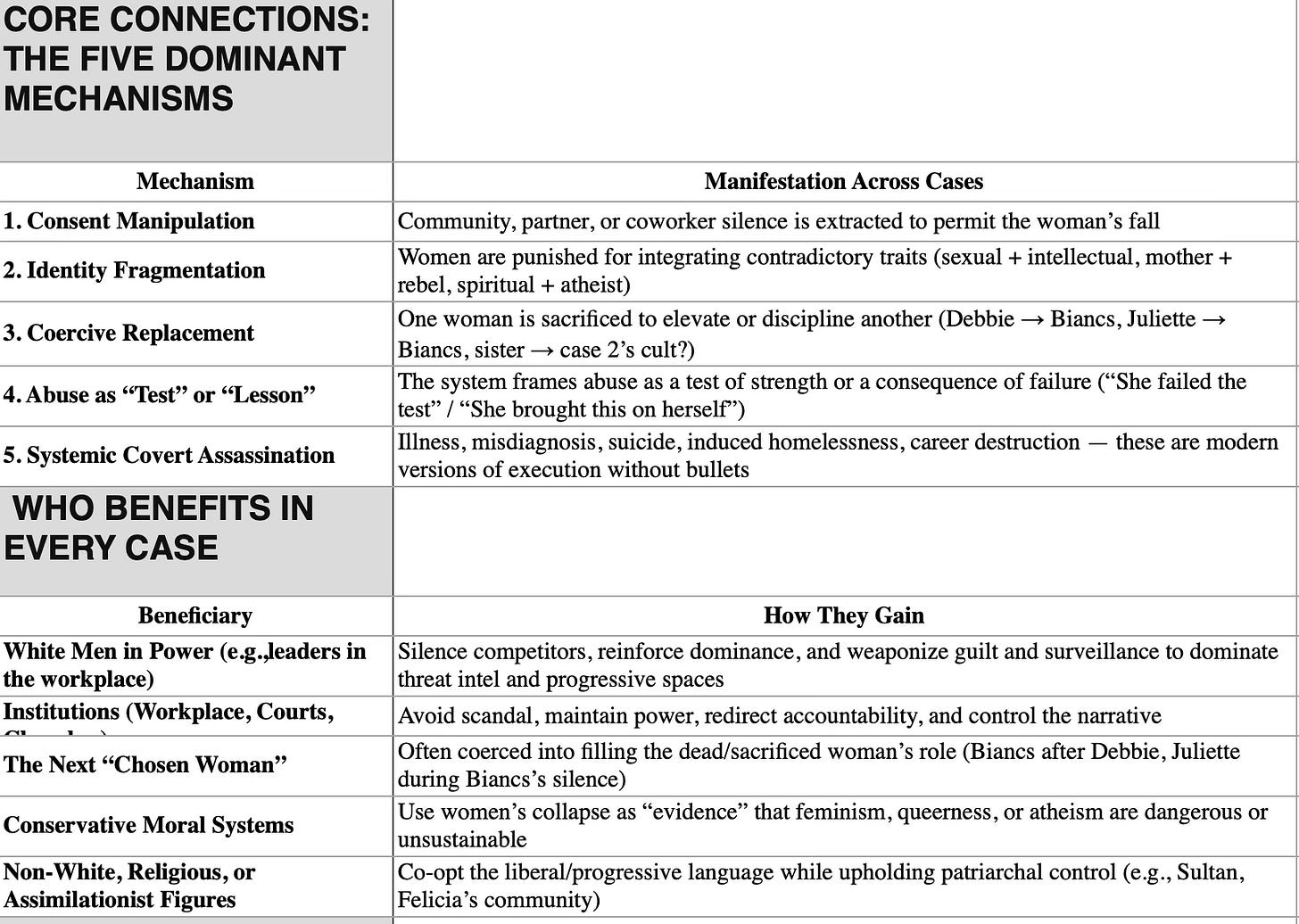
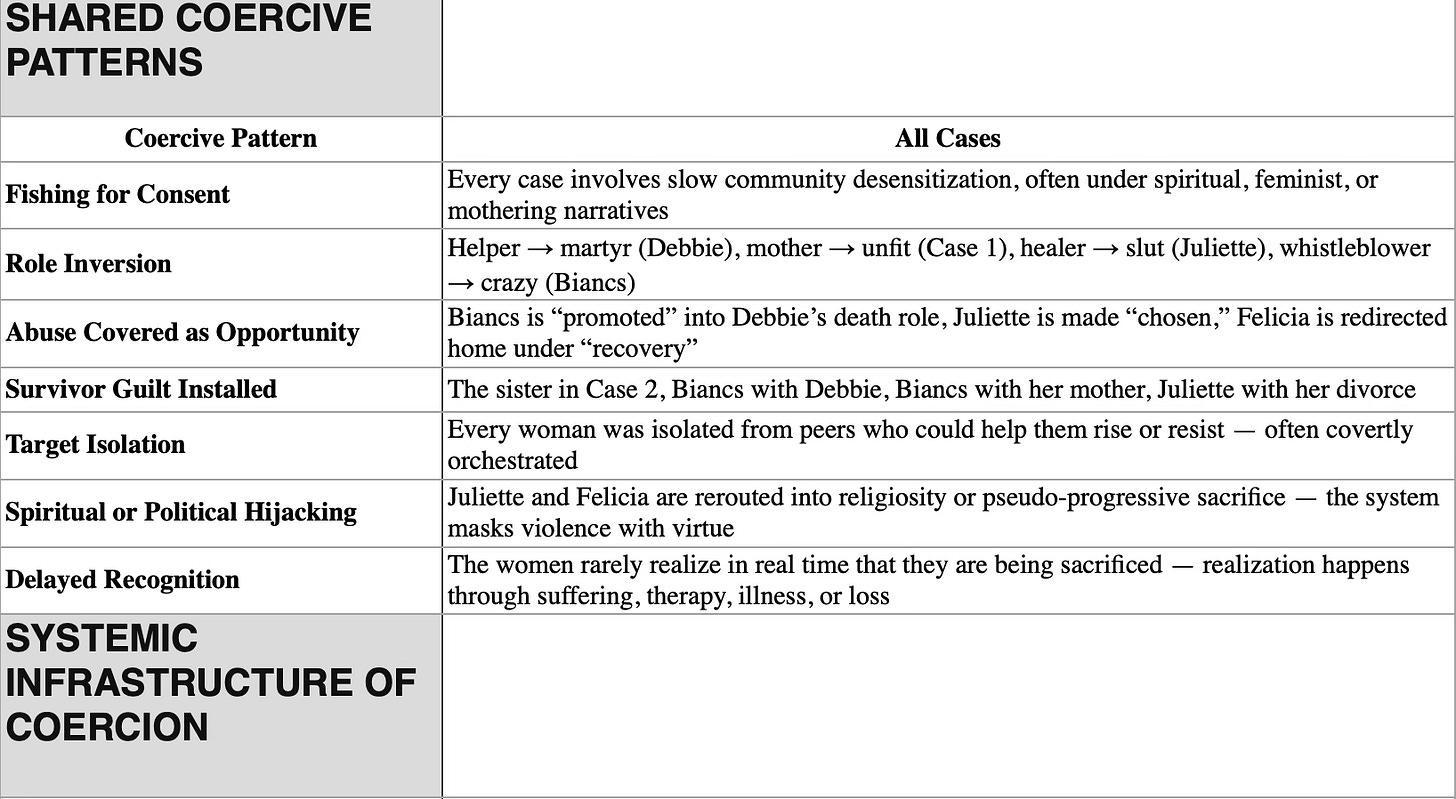
Drawing from your five dominant mechanisms, we can define the following “data classes” targeted for exfiltration:
The Beneficiaries: Who Receives the Exfiltrated Data
Your “WHO BENEFITS” table perfectly maps to the destinations of this stolen “data”:
People in Power / Institutions: Receive exfiltrated Consent & Social Sanction. They use this stolen social license to reinforce dominance and avoid accountability. The silence of the community is the data they needed.
The Next “Chosen Woman”: Receives exfiltrated Social Position & Legacy. She is implanted with the stolen social capital, but it comes pre-loaded with malware—the coercive conditions of her new role.
Conservative Moral Systems: Receive exfiltrated Narrative Autonomy. They take the stolen narrative (”her failure”) and use it as evidential data in their own propaganda campaigns against feminism, queerness, etc.
Assimilationist Figures: Receive exfiltrated Integrated Identity. They weaponize the fragmented identity pieces (”See, she couldn’t handle being both X and Y”) to police others within the community, enforcing narrow, “acceptable” roles.
Defensive Countermeasures: How to Secure the “Human System”
If these are the critical assets, how do we design defenses?
Encrypt Consent: Make community consent explicit, active, and revocable. Build cultures that reject tacit, fished-for approval. This secures the “consent data” against theft.
Air-Gap Identity: Foster environments where complex, integrated identities are celebrated, not punished. This makes “Identity Fragmentation” attacks harder to execute and the “data” less valuable to steal.
Segment the Social Network: Ensure that roles, mentorship, and legacy are community-held and not tied to a single individual who can be “replaced.” Use multi-signature authentication for succession (many must approve).
Write-Protect Personal Narratives: Create unwavering community norms that the target owns the definition of their experience. Publicly reject adversary-imposed narratives (”tests,” “lessons”). This is a data integrity control.
Back Up the Future: Systems must have robust recovery plans. This means tangible, rapid-response support for targets of sabotage—legal aid, financial grants, mental health care, and public re-entry advocacy—to restore the “system” after an attack.
A Pattern of Coercive Exfiltrations in Maryland: Anonymous Case Studies
Case 1: A Ukrainian-born woman in Maryland married to an Argentinian cis man with a large religious family, who held a fused American identity, faced a devastating coercive attack following her divorce. After a third party covertly invested in her ex-husband’s career, he leveraged his new position to weaponize the family court system and steal primary custody of their daughter. The attack targeted her most vital assets: her role as a mother and her health, manifesting in a diagnosis of vulva cancer and her daughter being turned against her. Despite the clear danger, she exhibited profound resistance to leaving Maryland, indicating successful coercion that bound her to the location of her abuse.
Case 2: A young, high-performing Black immigrant woman in Maryland was killed under suspicious circumstances believed to be linked to local power structures. Her surviving sister, also a high-performer trapped in a service role, carries the trauma of this loss compounded by a history of familial religious abuse. The sister lives with intense guilt, social isolation, and the conviction that her sister’s death involved progressive actors who chose abuse over protection, mirroring other cases in the region.
Case 3: A research engineer, known for her exceptional helpfulness, was coercively manipulated within a corporate environment. Her altruism was weaponized to pressure her into sacrificing her health and ultimately her life for the company’s benefit. Her death was then used to cover for institutional failures. A colleague who later assumed her role was not protected but was instead subjected to years of covert surveillance, sabotage, and psychological abuse designed to induce incapacity and self-doubt, following the same sacrificial blueprint.
Case 4: A group of Romanian immigrant women with careers in Washington D.C. institutions were systematically dragged down by coercive attacks. The pattern involved targeting their families (including children’s health), inducing illness in the women themselves, and engineering professional and financial instability. This forced disruptive life decisions, such as moving countries under duress rather than to locations that would aid recovery, demonstrating a successful campaign to derail their lives and potential.
Case 5: A threat hunter and single mother with a layered trauma history was targeted within the cybersecurity industry. The multi-year campaign included covert surveillance, reproductive coercion, career sabotage, and attacks designed to induce physical and mental illness. After she escaped the immediate environment, the coercion extended to weaponizing the family court system to steal custody of her child and continuing to target her child’s health, ensuring the attack persisted across geographic and professional boundaries.
Case 6: An LGBTQ+ advocate and humanist was brutally targeted in her workplace. The coercion was sexual and psychological in nature, designed to destroy her identity and autonomy. She was slut-shamed, coerced into acts of bestiality, and systematically broken until she was forced into a radical cult to “repent.” This case illustrates how coercive attacks can forcibly convert a progressive, independent individual into a symbol for regressive ideologies, serving as a warning to others.
Conclusion: From Detection to Asset Protection
Parts 1 and 2 of this series focused on detecting the adversary’s tactics and invisible signatures. Part 3 reveals the strategic objective: life exfiltration.
Understanding this shifts the defense paradigm. We are no longer just looking for strange processes on the system. We are identifying and securing our most critical assets: our right to our own consent, our complex selves, our stories, our roles, and our futures. By mapping the exfiltration goals, we move from personal resilience to designing inherently secure human systems where the adversary’s desired data is encrypted, segmented, backed up, and ultimately, not for sale.
The final step in the kill chain is not inevitable. We can design systems where exfiltration fails.