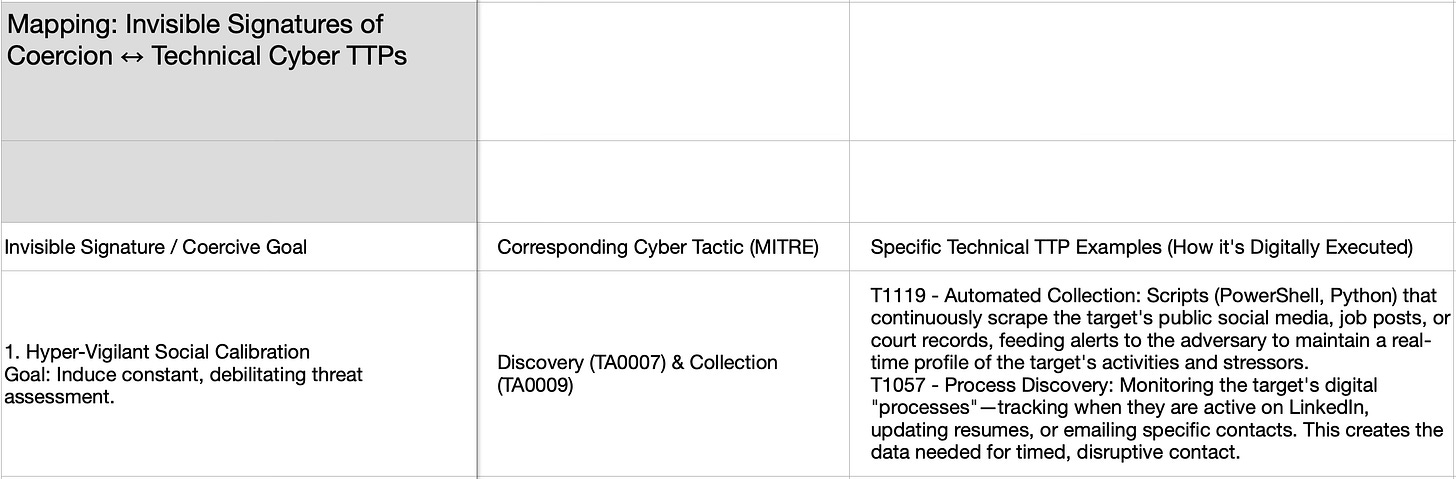
Part 4. Mapping the Adversary’s Playbook: From Invisible Human Psychological Signatures to Defendable Technical TTPs
Mapping coercive human behavior to cyber threat tactics techniques and procedures.
This is the final, critical step in operationalizing the framework. We are moving from the psychological and social TTPs to their technical execution layer. This mapping shows that the adversary’s goal (coercive control) can be achieved using the same technical infrastructure used for cyber-espionage or data theft.
Here is the mapping of Invisible Signatures to specific, real-world Cyber TTPs as cataloged in the MITRE ATT&CK® framework.
Integrated Scenario: “The Life Ransomware Attack”
Let’s see how these technical TTPs combine to execute a coercive campaign, using the provided case as an example.
Adversary Objective: Ensure the target remains isolated, unemployed, and unable to effectively fight a custody battle.
Phase 1: Discovery & Initial Access (Calibration & Mapping)
TTP: T1119 (Automated Collection) via a script monitoring the target’s LinkedIn, Indeed, and Pacer (court records) for activity.
Coercive Effect: The adversary knows the day she files a court motion or applies to a new job. This enables perfectly timed disruptive contact.
Phase 2: Persistence & C2 (Agency Compression)
TTP: T1071 (Application Layer Protocol) using a compromised, but seemingly normal, communication channel (e.g., her ex-husband’s email account is controlled by the adversary to send coercive messages).
Coercive Effect: She receives “legal advice” or threats from a familiar source, creating confusion and eroding her trust in her own judgment.
Phase 3: Lateral Movement & Collection (Weaponizing the Network)
TTP: T1566 (Phishing) emails sent to her listed references, potential landlords in Portland, or her friend Talia. The emails contain fabricated information about her mental state or legal status.
Coercive Effect: Her support network and opportunities are silently poisoned. Allies get strange warnings, references give lukewarm reviews, rental applications are denied. This induces Observer Amplification in allies (they get worried and chaotic) and Agency Compression in the target (her efforts mysteriously fail).
Phase 4: Impact & Exfiltration (Inducing Freeze & Stealing Narrative)
TTP: T1486 (Data Encrypted for Impact). A ransomware-locked ZIP file is emailed to her containing a subset of her own private photos/journal entries, with a note: “More where this came from. Stop your legal actions.”
T1048 (Exfiltration Over Alternative Protocol). Her private blog drafts are stolen via a keylogger and posted on a fringe forum to paint her as unstable.
Coercive Effect: This is a direct, digital assault to induce Freeze. It also exfiltrates and weaponizes her narrative. The dual threat of disclosure and loss paralyzes her decision-making.
Defensive Countermeasures (Applied Cybersecurity Wisdom)
For Hyper-Vigilance: Use canary tokens or deliberate misinformation. Plant false data points in your public profiles (e.g., a fake company name on your resume) to see who reacts, revealing the adversary’s collection nodes.
Against Agency Compression/C2: Segment your communications. Use one email for job search, another for legal, another for close allies. A compromise in one channel doesn’t give full C2. Use signal-based codes with allies (e.g., “If I say ‘the weather is green,’ I am under duress”).
Against Freeze/Impact: Air-gapped, encrypted, immutable backups. Keep your critical evidence (legal docs, portfolio, journal) on a physically separate drive (e.g., a VeraCrypt USB kept in a safe place). Ransomware cannot touch it.
Against Observer Weaponization: Pre-brief your allies. Give your core support network a secure briefing on the TTPs you face. “If you get a strange email about me, it’s likely phishing. Here’s my PGP key to verify.” This inoculates your human network.
Against Narrative Exfiltration: Control your own narrative preemptively. Publish your own story first, on your own terms, in a controlled venue. It’s much harder for an adversary to weaponize stolen data if you’ve already framed it publicly as evidence of the attack.
Conclusion: The tools of cyber intrusion are not just for stealing credit cards. They are the perfect, scalable infrastructure for psychological operations (PSYOPs) and social coercion. By mapping the coercive goals to specific, known-bad TTPs, we accomplish two things:
It demystifies the magic of the attack for the victim—it’s not omnipotence, it’s a toolkit.
It provides a clear defensive playbook grounded in decades of cybersecurity experience: segment, back up, monitor for IoCs (Indicators of Compromise), and inoculate your network. The battle is not just in the mind or the courtroom; it is also on the device, in the network, and in the data.